Documentation Index
Fetch the complete documentation index at: https://docs.replit.com/llms.txt
Use this file to discover all available pages before exploring further.
New to dependency security? See Security concepts for definitions of CVE, SBOM, exposure, Fix with Agent, Republish, and Auto-Protect.
How results are categorized
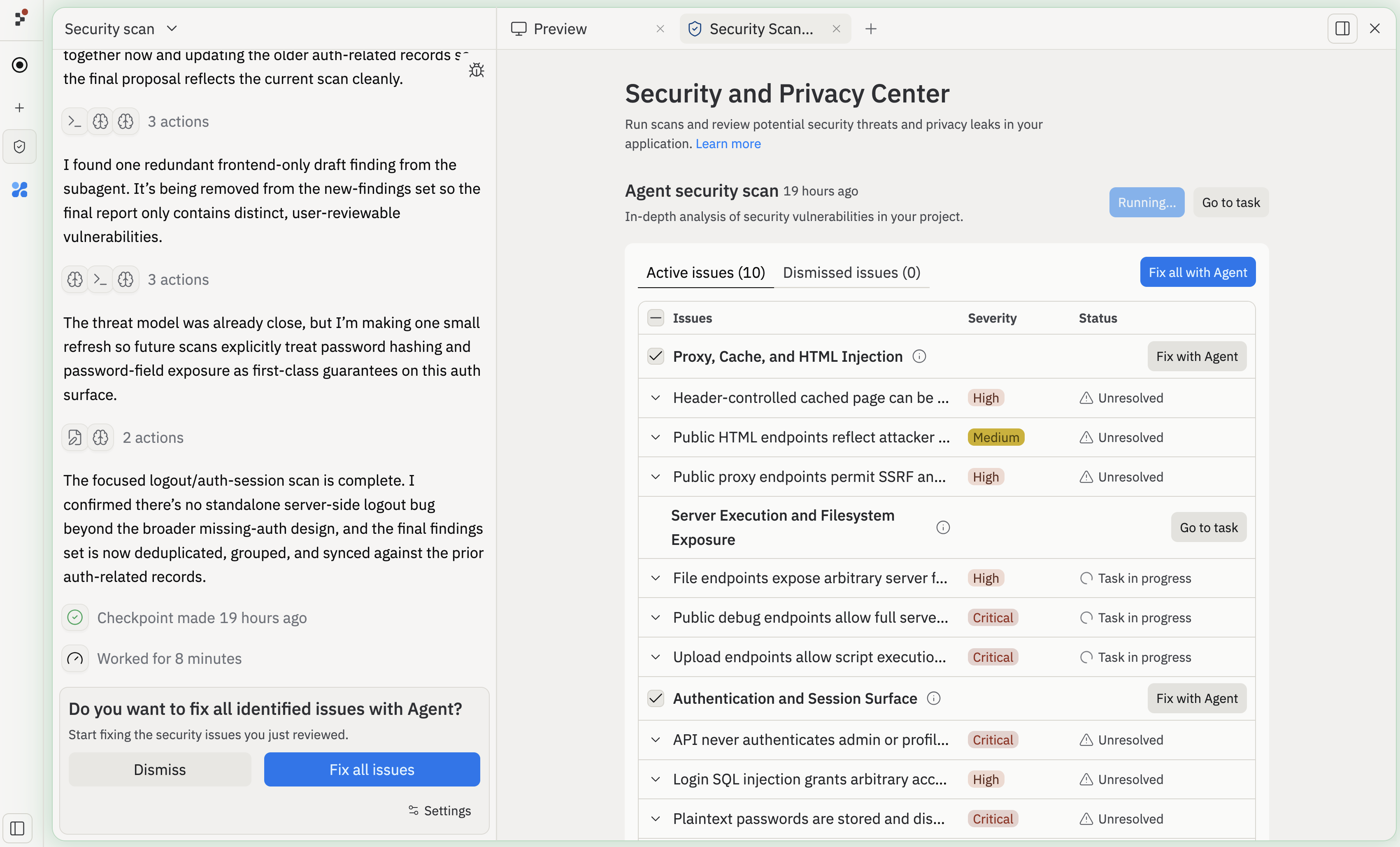
Results from both scan types appear in the Security pane, categorized by severity level:- Critical: Vulnerabilities that pose an immediate risk and should be addressed before publishing. Examples include remote code execution, SQL injection in exposed endpoints, and leaked credentials.
- High: Serious issues that could be exploited under certain conditions, such as cross-site scripting (XSS), insecure authentication flows, or unpatched dependencies with known exploits.
- Medium: Issues that represent a potential risk but are less likely to be exploitable, such as missing security headers or overly permissive CORS configurations.
- Low / Informational: Minor issues or best-practice recommendations, such as deprecated API usage or verbose error messages in production.
What is the Project Security Center?
The Project Security Center is your project’s central hub for finding and fixing security and privacy vulnerabilities before you publish. Open the Security pane in your Project to run scans, review findings, and send accepted issues to Agent for remediation. The Project Security Center supports two types of scans:- Automatic dependency scans: Free, lightweight scans that check project packages against public vulnerability records
- Agent security scans: AI-assisted reviews that combine model analysis with static code analysis tools to audit your entire codebase
Automatic dependency scans
Automatic dependency scans audit the packages your project depends on against public vulnerability records. These scans are free and run automatically. When a new Common Vulnerabilities and Exposures (CVE) entry is disclosed, Replit checks it against your project’s dependencies and surfaces any matches in the Security pane — no manual re-scan needed. Dependency scanning supports Node.js/npm, Python, Go, Rust, PHP, and Ruby. For example, a scan might flag a known vulnerability in an outdated package likeexpress@4.18.2.

Auto-Protect
Auto-Protect extends automatic dependency scanning. When a matching vulnerability is detected, Replit Agent prepares and tests a patch and emails you a direct link. Auto-Protect covers dependency CVEs only — for vulnerabilities in your application code, use Agent security scans. For each new vulnerability matched against your project’s dependencies, Replit:- Emails you a summary with a direct link to the affected project’s Security pane.
- Asks Replit Agent to prepare and test a patch that fixes the vulnerability.
- Leaves the patch pending your review in the Security pane.
Enable Auto-Protect
Both Auto-Protect settings are off by default. Enabling Auto-Protect requires two settings: one admin-only setting that authorizes Replit to prepare patches, and one personal setting that controls whether you receive emails about new vulnerabilities.Enable patch preparation (admin only)
Go to Settings > Account > Advanced and select the minimum severity (low, medium, high, or critical) at which Replit should automatically prepare remediations. Setting a higher threshold means Replit only prepares patches for the most serious vulnerabilities.
Agent-prepared remediations are billed like any other Agent work, even when
prepared proactively by Auto-Protect.
Agent security scans
Agent security scans go beyond dependency checks to perform a comprehensive audit of your entire codebase. Security Agent combines model-based review with static analysis tools like Semgrep and HoundDog.ai to find vulnerabilities that pattern-matching alone would miss. Agent security scans are available to all paid Replit builders. For larger projects, a deep audit can take up to 15 minutes to ensure a thorough assessment.What Security Agent does
When you start an Agent security scan, Security Agent performs a full review of your codebase:- Maps your architecture — identifies routes, APIs, data flows, and entry points
- Builds a threat model — creates a customizable threat modeling plan for your application
- Runs static analysis — uses Semgrep and HoundDog.ai to scan for code-level vulnerabilities and privacy issues
- Analyzes findings with AI — evaluates whether flagged issues are actually exploitable in your application’s context, significantly reducing false positives
- Generates a findings report — presents identified risks for your review
- Static analysis (SAST) issues: Insecure code patterns like SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF)
- Privacy issues: Sensitive data flowing into risky sinks like logs, files, or third-party APIs
- Architectural vulnerabilities: Security gaps in how your routes, APIs, and data flows are structured
Starting an Agent security scan
After the review completes, Security Agent generates a report of identified risks. You can review the vulnerability details, dismiss findings you understand and are willing to accept, or revise findings before sending them for remediation.
After you review the findings, send accepted issues to Replit Agent for remediation. Security Agent organizes vulnerabilities into separate tasks so Agent can work on multiple fixes in parallel. After fixes are applied, run another scan to confirm the issues are resolved.
After you fix the first set of findings, run another scan. Larger projects may reveal additional issues once higher-severity findings are resolved.
Limitations and best practices
- Privacy and data handling: All scanning runs on Replit infrastructure. Your code and data are not sent to Semgrep, HoundDog.ai, or other third parties. Scan configuration and results stay attached to your Replit App.
- Language support:
- Dependency scanning supports many popular ecosystems (including Node.js/npm, Python, Go, Rust, PHP, and Ruby).
- Automatic dependency fixing is currently focused on Node.js/npm.
- Not a full security review: Use scans alongside code review, tests, dependency review, and live app checks.
- Re-run after changes: Run a scan again after:
- Adding or updating dependencies
- Making major code changes
- Before publishing a new version
Publish checks
The Block publishing of critical vulnerabilities setting lives in the Deploy tab’s Advanced settings (and the Redeploy flow). Replit always runs a security scan before publishing; this toggle decides what happens when the scan finds a critical-severity issue:- On — publishing is blocked until the issue is resolved or dismissed.
- Off — publishing proceeds and the finding is surfaced for you to review.
This setting used to be labeled “Security scan before publishing” and carried a Beta tag. It’s now out of Beta and renamed to make the behavior clearer — the scan itself always runs either way.
Next steps
- Learn more about Publishing and how to publish your Replit App once scans are clean.
- Explore Replit Agent to fix security and privacy issues directly from the Project Editor.
- Read How Replit Secures AI-Generated Code for more on Replit’s approach to security.
- Check out Editor features for more tools to improve code quality, performance, and reliability.


